Protecting Your Software from Cyber Threats: Safeguarding Your Digital Fort
Are you worried about the safety of your digital assets in an increasingly interconnected world? You’re not alone. With cyber threats evolving and becoming more sophisticated, safeguarding your software has never been more crucial. This article will guide you through the essential steps to fortify your software and keep those digital threats at bay.
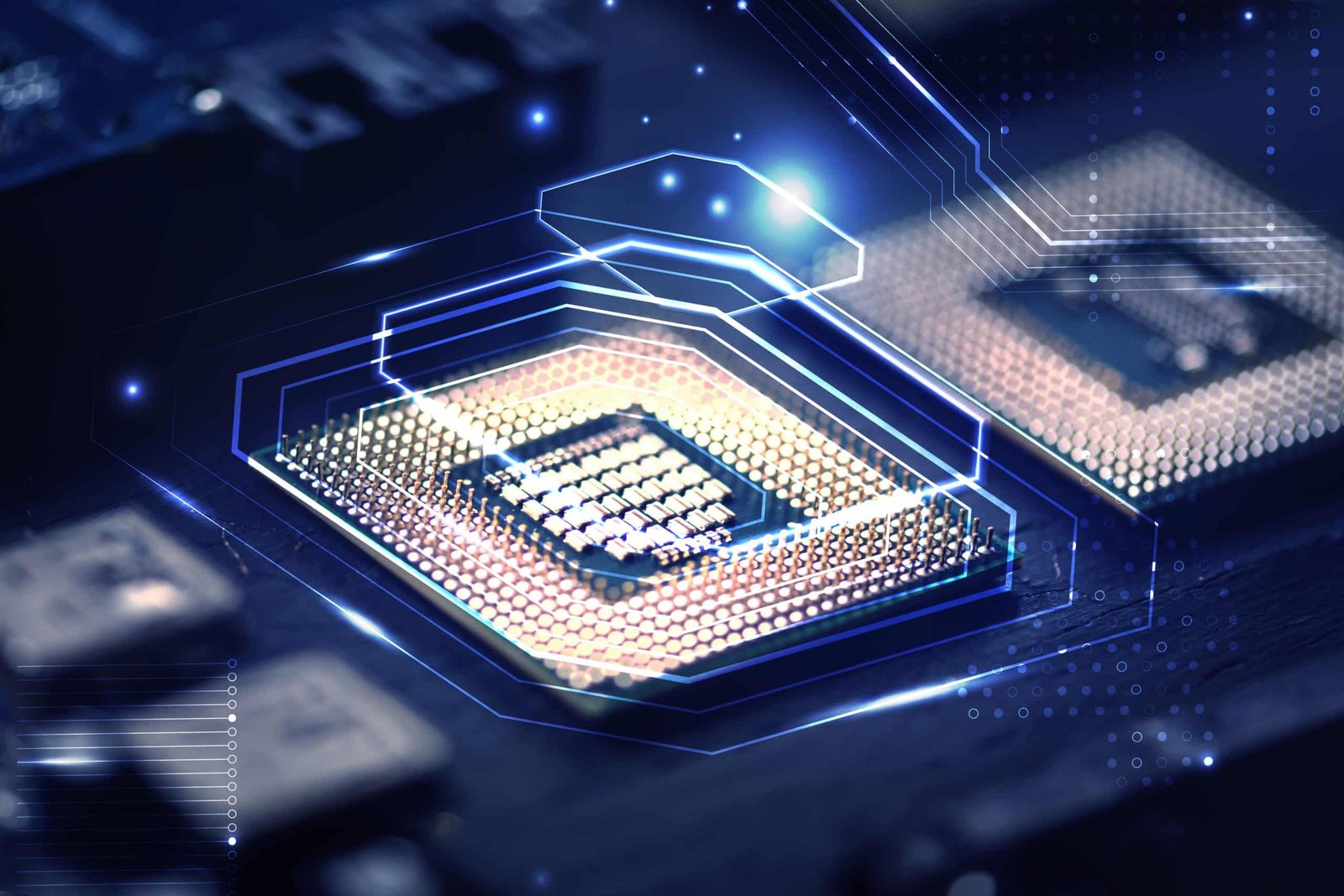
Understanding the Cyber Threat Landscape
Before we dive into protection strategies, let’s take a moment to understand the cyber threat landscape. It’s like navigating a digital battlefield where hackers and cybercriminals constantly seek vulnerabilities in your software to exploit. They can steal sensitive data, disrupt operations, and even hold your digital world hostage.
The Perplexity of Cyber Threats
The world of cyber threats is perplexing. It’s a maze of malicious code, phishing attempts, ransomware attacks, and more. These threats can infiltrate your software unexpectedly, making it crucial to stay vigilant. But don’t worry; we’ve got you covered with expert advice.
Building Strong Digital Defenses
Imagine your software as a fortress and your data as the treasure within. To protect it, you need robust defences. Here’s how to fortify your digital fort:
1 Keep Software Updated
Like a castle’s walls need regular maintenance, your software needs updates. Software developers release patches to fix vulnerabilities, so keep everything up-to-date.
2 Strong Passwords
Think of your passwords as the keys to your digital kingdom. Create complex, unique passwords and change them regularly. Consider using a password manager to keep track of them.
3 Firewalls and Antivirus Software
These are like the moat around your castle. Firewalls and antivirus software can help block malicious traffic and detect threats before they breach your defences.
4 Employee Training
Even the strongest fortress can fall if the guards are not vigilant. Educate your employees about cyber threats, phishing, and social engineering tactics.
5 Regular Backups
Just as you’d protect valuable artefacts, regularly back up your data; this way, even if your defences are breached, you can recover your precious information.
The Burstiness of Cyber Attacks
Cyber attacks can burst into your life at any moment. They’re unpredictable and can cause chaos in seconds. Following the steps above, you’ll be better prepared to withstand these bursts and ensure your digital assets remain intact.
Conclusion: Be the Digital Knight
In the digital age, protecting your software is like being a knight guarding a medieval fortress. You can defend your digital kingdom against cyber threats with the right tools and strategies. Remember, it’s not a matter of if but when these threats will come knocking.
And be sure to explore Magque, your go-to source for the latest and most intriguing updates in the realms of informative tips & reviews!
FAQs
Q1. What are the common types of cyber threats that can target my software?
Cyber threats include viruses, malware, ransomware, phishing attacks, and DDoS (Distributed Denial of Service) attacks. It’s essential to understand these threats to protect your software better.
Q2. How can I keep my software and data safe from cyber threats?
To safeguard your software, keep it updated with the latest security patches, use strong passwords, employ firewalls and antivirus software, educate your team about potential threats, and regularly back up your data.
Q3. Are there any specific cybersecurity best practices for businesses?
Yes, businesses should establish a cybersecurity policy, conduct regular security audits, implement network segmentation, and invest in employee training. Having an incident response plan is crucial in case of a security breach.
Q4. What should I do if my software becomes a victim of a cyber attack?
If your software falls victim to a cyber attack, disconnect affected devices from the network, report the incident to your IT department or a cybersecurity expert, and follow your organization’s incident response plan. Do not pay ransoms to cybercriminals.
Q5. How can I stay updated on cybersecurity threats and trends?
Staying informed is essential. You can subscribe to cybersecurity news websites, follow reputable cybersecurity experts on social media, and participate in webinars and conferences related to cybersecurity. Additionally, consider joining industry-specific forums or associations for insights and networking opportunities.
Read Also This :- Securing Your Network Against Cyber Threats